SCADA Cyber Security For Water and Wastewater Systems
There is a great need to secure your SCADA systems against cyber attacks. We have seen the effects of cyber attacks on water and wastewater systems, and the need to secure your data and systems as quickly as possible. Here are a few tips to safeguard your water and wastewater systems from cyber threats. Also, keep in mind that the importance of server-centric architecture is paramount. With these tips, you can protect your system and react quickly to a situation where something goes wrong.
Impact of cyber-attacks on water and wastewater systems
There are several types of attacks that can cause damage to water and wastewater systems. The cyber-attacks may disrupt the operating system, while air-to-surface missile attacks will target an isolated component of infrastructure. Explosive weapons, such as cluster bombs, use both high and low-explosive materials to cause damage. These weapons often fragment to cause the desired effect. In addition to the blast, the high-explosive substances cause heat and damage to water and wastewater systems.
While water and wastewater systems are highly vulnerable to cyber-attacks, the water and wastewater sector needs new thinking and greater resources to manage the risks. The water sector needs guidance and education in the field of information security, and it needs to adopt new technologies to improve security. In addition to increased resources, the water and wastewater sector also needs new thinking to address cyber-attacks and integrate information technology into their operations.
The impact of cyber-attacks on water and wastewater system operations is growing. In the past year, a disgruntled contractor used radio commands to control a wastewater plant in Norway, causing 800,000 litres of raw sewage to spill, killing marine life. In the United States, a hacktivist group gained access to a water utility and manipulated the flow of chemicals twice.
Need for a server-centric architecture in SCADA systems
The SCADA network layer supports remote firmware update management, alarm notification, and data storage. While this layer is critical for process control and operator access, it often communicates with devices in lower-trust layers. It is important that access to this layer be limited to domain controllers and SCADA servers. Moreover, this layer should only be accessible through a dedicated DMZ (distributed management zone).
A server-centric architecture provides higher security as it eliminates single points of failure. A server-centric architecture also reduces system costs. In contrast, traditional SCADA solutions require additional set-up, including radio networks, cellular modems, and a separate cell service plan. These systems can become costly and difficult to maintain. Therefore, a server-centric architecture is the best option.
Next-generation SCADA equipment supports TCP/IP and UDP. It can operate over satellite, cellular, and private radio networks. It can also act as an Ethernet Serial gateway that enables legacy serial equipment to connect to TCP/IP networks. Additionally, it can be used with host software such as NETSCADA to implement powerful IP-based SCADA networks over landlines and mixed cellular systems.
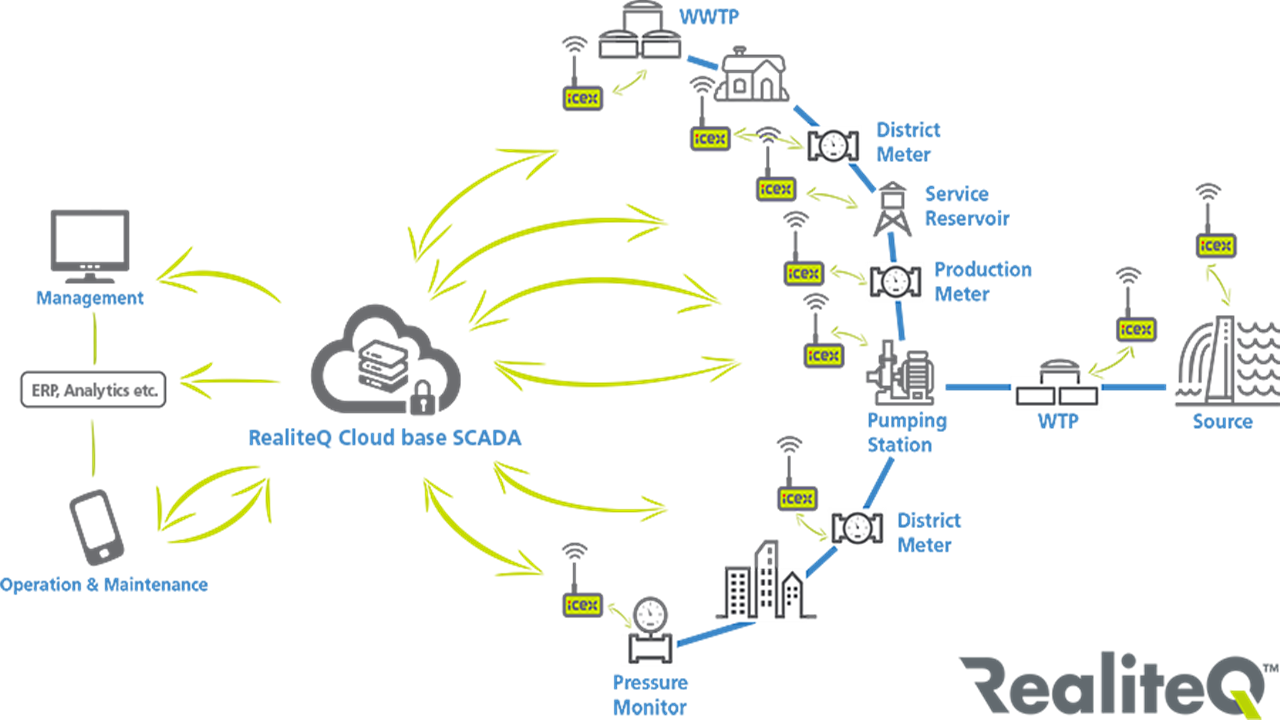
SCADA systems for water and wastewater systems have three levels. The lower level contains pumping stations, reservoirs, and monitoring sensors. The middle layer contains SCADA servers, a PLC network, and a DMZ. The upper layer is the decision-making level of the regional SCADA system. It manages communications with the lower-level SCADA systems and controls, as well as data processing in real-time.
A server-centric architecture for SCADA systems for water and wastewater systems is essential to ensure optimal performance. It provides a unified solution for all users and ensures that all processes are consistent. It also provides a centralized database for monitoring and data sharing. In addition, it enables remote monitoring and management of operations and maintenance. It is also a good way to ensure security.
A server-centric architecture is also essential for maintaining data integrity. A server-centric architecture supports multiple remote systems. CSWorks offers a server-centric architecture. The framework allows application engineers to mix and match products from multiple vendors, enabling them to develop more flexible and powerful applications. Furthermore, open standards protect automation investments from the obsolescence of proprietary technologies. This means that they can be upgraded to more advanced systems without worrying about their security.
A server-centric architecture also supports flexible design and rapid deployment. For example, a “one4all” tool could generate all the necessary views for an entire SCADA project. This would eliminate the need for user management. It would also allow system administrators to create multiple customized views for different users. The tool that generated these windows should also support SCADA clients. A server-centric architecture is also easier to manage than a client-centric one.
Need for quick response when something goes wrong
While there are many SCADA security challenges, the government has taken several steps to advance the field. Among them are increased funding for R&D and strengthened industry-government partnerships. These efforts are already making progress, but there is still much to be done. It is imperative that we maintain the momentum of our current R&D and funding efforts, and do not interrupt ongoing programs. For example, the DOE Control Systems Roadmap and the DHS Process Control Systems Forum are important sources of coordination between government, industry, and other infrastructures.
Another important step towards increasing SCADA cyber security is to improve the overall system’s connectivity. Often, SCADA systems communicate over dial-in telephone modems, which exposes them to major vulnerabilities. Many SCADA systems lack encryption technology or password protection for sensitive data. They are also susceptible to attacks by nation-states and hackers without control systems engineering training. In addition, these systems are exposed to the inherent vulnerabilities of interconnected computer networks. Common threats include worms and viruses and network flooding.
Increasing cyber awareness has led to reassessment of facility operations. The CSSC is now involved in testing and assessment of major control systems SCADA vendors. As a result, the vendors have taken measures to minimize vulnerabilities and share information with users. As a result, the public can benefit from more comprehensive protection against cyber attacks. When a security incident occurs, a quick response is critical.
Another critical need is enhancing the awareness of threats and vulnerabilities in SCADA systems. In addition, critical infrastructure owners and operators need to increase training and information on cyber security for control systems. The consequences of a SCADA cyber attack are numerous and varied. While there have been no known major incidents involving SCADA systems, the threat remains high. For example, if a cyber attack targets a system, the public could face disastrous consequences.
Developing a comprehensive SCADA cyber security strategy is important for water and wastewater systems. Fortunately, there are many resources available to protect these critical systems. The National Computer Emergency Readiness Team (USER) and the National Cyber Security Division are working on the problem together. By working with industry experts, they are developing standards and implementing mitigations that will protect SCADA systems and help organizations respond more quickly when something goes wrong.
While there are no federally mandated standards for SCADA cyber security, there are many resources available to help water and wastewater systems protect themselves. For example, the US-CERT CSSC has created several test beds to help the industry develop cyber security for water and wastewater systems. These test beds provide a centralized response in the event of a cyber attack. Further, CSSC provides a comprehensive and coordinated approach to SCADA cyber security, combining the expertise and facilities of the US-CERT.
We are fully capable of helping you with saving your SCADA systems against cyber attacks. Get a Free Consultation now. We are just a Call Away.


